What is the Deep Web? Beyond Google, It's Your Everyday Data
Imagine the internet as a vast, boundless ocean. When you type a query into Google or Bing, you're essentially skimming the surface, catching only the sunlit ripples. This visible portion, often called the Surface Web, represents a tiny fraction – less than 0.3% – of all the information available online. Out of an estimated 550 billion pages, traditional search engines only index a mere 2 billion. For a truly comprehensive view of the digital landscape, you need to dive deeper, into what is known as the Deep Web Net. Far from being a sinister underworld, the Deep Web is an essential, often overlooked, and incredibly expansive part of our daily online experience, making up an astonishing 90-95% of the entire World Wide Web.
The term "Deep Web" often conjures images of clandestine activities and shadowy figures. However, this perception is largely a misconception fueled by sensationalism. In reality, the vast majority of the Deep Web consists of perfectly legitimate, everyday data that simply isn't indexed by standard search engines. It's the private corners of the internet that require a login, a password, or a specific query to access. Understanding the true nature of the Deep Web is crucial to demystifying the internet's hidden layers and appreciating the privacy and security mechanisms that underpin our digital lives.
Beyond the Surface: The Immense Scope of the Deep Web Net
The internet we interact with daily via search engines is like the tip of an iceberg. Below the surface lies an enormous repository of information, the Deep Web, that Google's crawlers cannot reach. The reason for this inaccessibility is not due to secrecy, but rather practicality and security. Search engines rely on links to discover and index content. If a page isn't linked from another publicly accessible page, or if it requires specific authentication, it remains outside the scope of traditional indexing.
Consider the sheer volume: estimates suggest the Deep Web is 400 to 5,000 times larger than the Surface Web. This isn't just a slightly larger pool; it's an entirely different ocean. From your personal email inbox to your online banking portal, from private cloud storage to subscription-based academic journals, these are all components of the Deep Web. They are dynamic, personalized, and often behind a protective barrier, designed to keep your information secure and relevant only to you or authorized parties. The Deep Web Net is thus not an alternative internet, but rather the majority of the internet, structured for privacy and specific access.
Unpacking the Deep Web Net: What Resides Within?
The greatest misconception surrounding the Deep Web is its association with illicit activities. While a tiny fraction of the Deep Web (the Dark Web) does host such content, the overwhelming majority is innocuous and vital to modern living. Here's a glimpse into the everyday data that forms the bulk of the Deep Web Net:
- Personal Email Accounts: Your Gmail, Outlook, or Yahoo Mail inbox is a prime example. You need a username and password to access it, making it part of the Deep Web.
- Online Banking Portals: Your bank statements, transaction history, and funds are all securely nestled within the Deep Web, protected by rigorous authentication.
- Social Media Private Content: While your public profile might be indexed, your private messages, hidden photos, and personalized news feeds on platforms like Facebook or Instagram are Deep Web content.
- Streaming Services: Your Netflix watch history, Spotify playlists, and Amazon Prime Video library all require a login, making them part of the Deep Web.
- Cloud Storage: Documents on Google Drive, Dropbox, or OneDrive that are shared only with specific individuals or kept private are Deep Web data.
- Private Company Intranets and Databases: Corporate networks, internal documents, and proprietary databases that require employee credentials are classic examples.
- E-commerce Shopping Carts and Order Histories: The items you’ve added to your cart on Amazon or your past orders are specific to your authenticated session.
- Academic and Research Databases: Many scholarly articles, journals, and scientific data are behind paywalls or institutional logins.
In essence, if you need to log in, fill out a form, or make a specific query to access information, you're likely interacting with the Deep Web. These pages are often dynamically generated, meaning their content changes based on user input or specific conditions, further hindering search engine indexing. This structure is not about hiding information for nefarious purposes, but about ensuring privacy, personalization, and security for billions of users worldwide.
Accessing the Deep Web Net: Easier Than You Think
The idea of "accessing the Deep Web" might sound like a clandestine operation, but in reality, you likely do it multiple times a day without even realizing it. The threshold for entering the Deep Web Net is simply the requirement of authentication or a direct link to dynamic content. When you log into your email, check your bank balance, or stream a movie, you are actively engaging with the Deep Web.
The distinction from the Surface Web lies in its accessibility. Public webpages are open for anyone to view and are designed for search engine discovery. Deep Web pages, on the other hand, are guarded by digital gates – be it a login screen, a CAPTCHA, or a direct link to a database query result. This makes the Deep Web not a separate network, but rather a functional segment of the internet where information is compartmentalized for specific, authorized users. There's no special browser required for most of the Deep Web, just your standard web browser and the correct credentials.
The Deep Web vs. The Dark Web: A Crucial Distinction
One of the most persistent confusions revolves around the terms "Deep Web" and "Dark Web." While the Dark Web is technically a tiny subset of the Deep Web, they are not synonymous. Understanding this difference is paramount to accurately perceiving the internet's hidden layers. The Internet's Hidden 95%: Demystifying the Deep Web, delves further into the scale of this vast network.
The Deep Web Net, as discussed, is comprised of all internet content not indexed by standard search engines, requiring authentication or direct access. It's largely mundane, legitimate, and essential data.
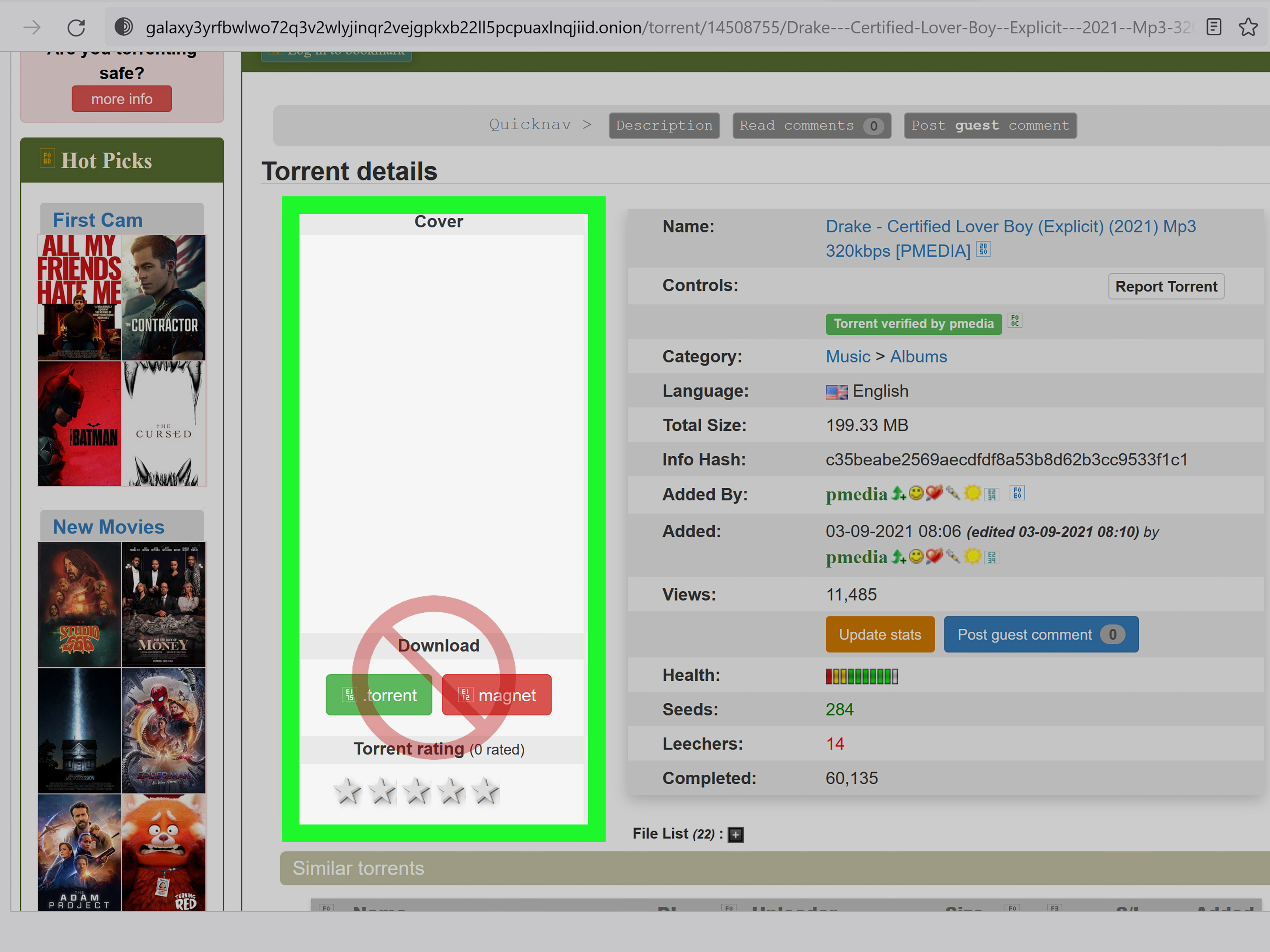
The Dark Web, conversely, is a small, intentionally hidden portion of the Deep Web. It requires specific software, configurations, or authorization to access, most famously the Tor (The Onion Router) browser. Its primary characteristic is anonymity, routing internet traffic through multiple relays to obscure a user's identity and location. While it can be used for legitimate privacy and activism, it has also become a haven for illegal activities due to this anonymity. This deliberate obscurity sets it apart from the general Deep Web, whose content is merely unindexed, not necessarily hidden. For a more detailed breakdown, explore Deep Web vs. Dark Web: Understanding Their Key Differences.
Securing Your Deep Web Net Footprint
Given that your most sensitive data resides within the Deep Web Net, safeguarding your accounts is paramount. While the Deep Web itself isn't inherently dangerous, compromised credentials can expose your personal information to significant risks. Here are practical tips to protect your Deep Web footprint:
- Strong, Unique Passwords: Use complex passwords for each online account. Avoid reusing passwords across different services. A password manager can be an invaluable tool for this.
- Enable Two-Factor Authentication (2FA): Wherever possible, activate 2FA. This adds an extra layer of security, typically requiring a code from your phone or a hardware token in addition to your password.
- Be Wary of Phishing: Always double-check the sender and URL of emails asking for your login details. Legitimate services will rarely ask for your password via email.
- Review Privacy Settings: Regularly audit the privacy settings on your social media, cloud storage, and other personal accounts to control what information is accessible and to whom.
- Use a Virtual Private Network (VPN): While not strictly for accessing the Deep Web, a VPN encrypts your internet connection, adding a layer of privacy and security to all your online activities, including when you log into your Deep Web accounts.
- Keep Software Updated: Ensure your operating system, web browser, and security software are always up-to-date to protect against known vulnerabilities.
Conclusion
The Deep Web Net, far from being a mysterious, dangerous entity, is the functional backbone of our modern internet experience. It's the vast repository of private, personalized, and dynamically generated information that underpins everything from your email to your online banking. By understanding that the Deep Web is primarily composed of everyday data and distinguishing it from the nefarious Dark Web, we can shed light on its true nature and appreciate its indispensable role in protecting our digital privacy and security. You engage with the Deep Web every single day, making it an undeniable and essential part of your online life, quietly working beyond the public gaze of search engines.